Automatically Scan Unrecognized and Quarantined Files
- Click 'Settings' > 'File Rating' > 'File Rating Settings'
- CCS can periodically re-scan unknown and quarantined files to check whether a new trust rating is available for them.
- This area lets you specify a schedule and settings for these scans.
File Rating
- CCS checks files when they are opened and rates them as 'trusted', 'malicious' or 'unrecognized'.
- The rating is obtained by checking the file's reputation on our master whitelist and blacklist.
- If no rating is available then CCS checks the trust rating of the software vendor.
- CCS will apply the vendor’s reputation to the file if one exists. CCS first checks the vendor's local reputation in the 'Vendor List'. If no local rating is available then it checks the file lookup service.
There are two ways a file can get an 'unrecognized' rating:
-
Because there is no rating for the file on Comodo's black or whitelists, and no user has assigned a malicious/trusted rating to the file.
OR
2. Because an admin, user or Comodo specifically assigned an 'unrecognized' rating to the file.
To view the rating:
- Go to 'Settings' > 'File Rating' > 'File List' > select an unrecognized file > Click 'File Details'
- Click
the 'File Rating' tab
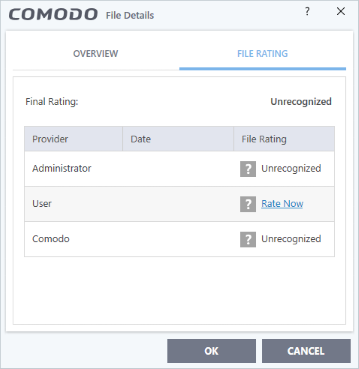
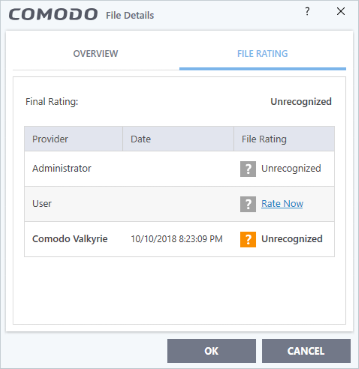
The following examples show files with and without ratings:
|
|
CCS will handle unrecognized files differently depending on whether the rating was proactively applied or not:
- Files awarded an unrecognized rating by admin, user or Comodo are not uploaded to Valkyrie.
- All other unrecognized files are uploaded to Valkyrie when executed or discovered by a rating scan. You can also submit them manually.
Regardless of the above, all unrecognized files are run in the container by default. If required, you can change auto-containment rules in 'Settings' > 'Containment' > 'Auto-Containment'. See 'Auto-Containment Rules' for more information.
Quarantined Files
- The antivirus scanner moves threats to quarantine to prevent them from infecting your system.
- All files in quarantine are encrypted, so they cannot run or cause harm.
- You can also manually move suspicious items to quarantine. See Manage Quarantined Items for more details.
Configure scan settings for unrecognized and quarantined files
- Click 'Settings' on the CCS home screen
- Click 'File Rating' > 'File Rating Settings'

- Automatically scan unrecognized files at equal intervals - CCS will check Comodo's master database to see if a new trust rating is available for unrecognized files. (Default = Enabled and set for every 4 hours)
- Automatically re-evaluate quarantined files at equal intervals - CCS will check Comodo’s master database to see if a new trust rating is available for quarantined files. (Default = Enabled and set for once everyday)
- Click 'Edit scan options' to open the unrecognized / quarantined scan profile:
Unrecognized Files Scan

Quarantined Files Scan
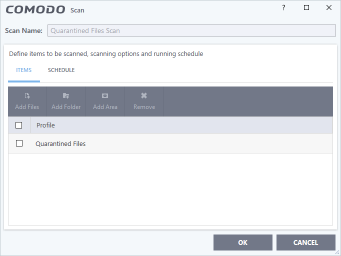
- Scan Name - The label of the scan. This is pre-configured and cannot be edited.
- Items - The files that are scanned by the profile. ‘Unrecognized’ and ‘Quarantined’ files are the defaults. You cannot edit or add files to this profile.
- Scan Options - (unrecognized files scan only) Configure scan technologies, how to handle threats, and more. See Configure scan options for the profile in the previous section for help with this.
- Schedule - Specify the frequency of the scans. See Configure a scan schedule in the previous section if you need help with this. (Default = Every 4 hours for unrecognized files scan and once in a day for quarantined files scan).
- Click 'OK' to save your changes.
- Click 'OK' in the 'Advanced Settings' screen for your settings to take effect.