HIPS Settings
- Click 'Settings' > 'HIPS' > 'HIPS Settings'
- HIPS settings let you enable/disable HIPS, set HIPS security level, and configure the general behavior of the HIPS module
Open the 'HIPS Settings' panel
- Click 'Settings' on the CCS home screen
- Click 'HIPS' > 'HIPS Settings'
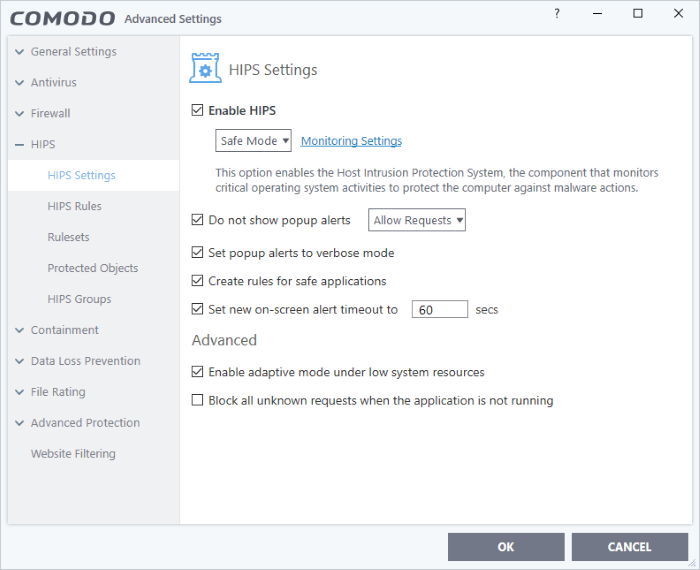
If enabled, you can configure the HIPS security level and monitoring settings:
Configure
HIPS Security Level
- Choose the security level from the drop-down under the 'Enable HIPS' check-box:
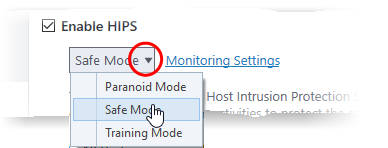
The choices available are:
- Paranoid
Mode: This is the highest security level setting and means that HIPS monitors and controls all executable files apart from those that you have deemed safe. Comodo Client Security does not attempt to learn the behavior of any applications - even those applications on the safe list and only uses your configuration settings to filter critical system activity. Similarly, CCS does not automatically create 'Allow' rules for any executables - although you still have the option to treat an application as 'Trusted' at the HIPS alert. Choosing this option generates the most amount of HIPS alerts and is recommended for advanced users that require complete awareness of activity on their system.
- Safe Mode: While monitoring critical system activity, HIPS automatically learns the activity of executables and applications certified as 'Safe' by Comodo. It also automatically creates 'Allow' rules for these activities, if the checkbox 'Create rules for safe applications' is selected. For non-certified, unknown, applications, you will receive an alert whenever that application attempts to run. Should you choose, you can add that new application to the HIPS rules list by choosing 'Treat as' and selecting 'Allowed Application' at the alert with 'Remember my answer' checked. This instructs the HIPS not to generate an alert the next time it runs. If your machine is not new or known to be free of malware and other threats then 'Safe Mode' is recommended setting for most users - combining the highest levels of security with an easy-to-manage number of HIPS alerts.
- Training Mode: HIPS monitors and learns the activity of any and all executables and creates automatic 'Allow' rules until the security level is adjusted. You do not receive any HIPS alerts in 'Training Mode'. If you choose the 'Training Mode' setting, we advise that you are 100% sure that all applications and executables installed on your computer are safe to run.
Configure
Monitor Settings
- Click the Monitoring Settings link to select the activities and objects that should be monitored by HIPS
|
Note: The settings you choose here are universally applied. If you disable monitoring of an activity or object here, it completely switches off monitoring of that activity on a global basis - effectively creating a universal 'Allow' rule for the activity. This 'Allow' setting over-rules any specific 'Block' or 'Ask' setting for the activity that you may have created in the 'Access Rights' and 'Protection Settings' interface. |
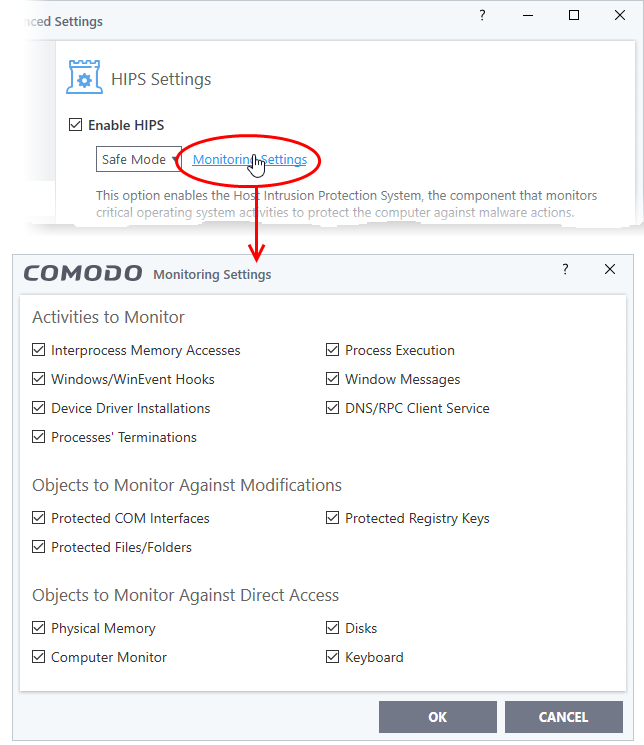
- Interprocess Memory Access - Malware programs use memory space modification to inject malicious code for numerous types of attacks. These include recording your keyboard strokes; modifying the behavior of applications and stealing data by sending confidential information from one process to another. One of the most serious aspects of memory-space breaches is the ability of the offending malware to take the identity of a compromised process to 'impersonate' the application under attack. This makes life harder for traditional virus scanning software and intrusion-detection systems. Leave this box checked and HIPS alerts you when an application attempts to modify the memory space allocated to another application (Default = Enabled).
- Windows/WinEvent Hooks - In the Microsoft Windows® operating system, a hook is a mechanism by which a function can intercept events before they reach an application. Example intercepted events include messages, mouse actions and keystrokes. Hooks can react to these events and, in some cases, modify or discard them. Originally developed to allow legitimate software developers to develop more powerful and useful applications, hooks have also been exploited by hackers to create more powerful malware. Examples include malware that can record every stroke on your keyboard; record your mouse movements; monitor and modify all messages on your computer and take remote control of your computer. Leaving this box checked means that you are warned every time a hook is executed by an untrusted application (Default = Enabled).
- Device Driver Installations - Device drivers are small programs that allow applications and/or operating systems to interact with hardware devices on your computer. Hardware devices include your disk drives, graphics card, wireless and LAN network cards, CPU, mouse, USB devices, monitor, DVD player etc. Even the installation of a perfectly well-intentioned device driver can lead to system instability if it conflicts with other drivers on your system. The installation of a malicious driver could, obviously, cause irreparable damage to your computer or even pass control of that device to a hacker. Leaving this box checked means HIPS alerts you every time a device driver is installed on your machine by an untrusted application (Default = Enabled).
- Processes' Terminations - A process is a running instance of a program. (for example, the Open VPN GUI process is called 'openvpn.exe'. Press 'Ctrl+Alt+Delete' and click on 'Processes' to see the full list that are running on your system). Terminating a process, obviously, terminates the program. Viruses and Trojan horses often try to shut down the processes of any security software you have been running in order to bypass it. With this setting enabled, HIPS monitors and alerts you to all attempts by an untrusted application to close down another application. (Default = Enabled).
- Process Execution - Malware such as rootkits and key-loggers often execute as background processes. With this setting enabled, HIPS monitors and alerts you to whenever a process is invoked by an untrusted application. (Default = Enabled)
- Windows Messages - This setting means Comodo Client Security monitors and detects if one application attempts to send special Windows Messages to modify the behavior of another application (e.g. by using the WM_PASTE command). (Default = Enabled)
- DNS/RPC Client Service - This setting alerts you if an application attempts to access the 'Windows DNS service' - possibly in order to launch a DNS recursion attack. A DNS recursion attack is a type of Distributed Denial of Service (DDoS) attack whereby a malicious entity sends several thousand spoofed requests to a DNS server. The requests are spoofed so that they appear to come from the target or 'victim' server but in fact come from different sources - often a network of 'zombie' PCs which are sending out these requests without their owners' knowledge. The DNS servers are tricked into sending all their replies to the victim server - overwhelming it with requests and causing it to crash. Leaving this setting enabled prevents malware from using the DNS Client Service to launch such an attack. (Default = Enabled)
|
Background Note: DNS stands for Domain Name System. It is the part of the internet infrastructure that matches a familiar domain name, such as 'example.com' to an IP address like 123.456.789.04. This is essential because the internet routes messages to their destinations using these IP addresses, not the domain name you type into your browser. Whenever you enter a domain name, your internet browser contacts a DNS server and makes a 'DNS Query'. In simple terms, this query is 'What is the IP address of example.com?'. The DNS server replies to your browser, telling it to connect to the IP in question. |
Objects To Monitor Against Modifications:
- Protected COM Interfaces - HIPS monitors the COM interfaces you specified from the COM Protection pane. (Default = Enabled)
- Protected Registry Keys - HIPS monitors the the Registry keys you specified from the Registry Protection pane. (Default = Enabled)
- Protected Files/Folders - HIPS monitors the files and folders you specified from the File Protection pane. (Default = Enabled)
Objects To Monitor Against Direct Access:
- Whether or not Comodo Client Security should monitor access to system critical objects on your computer. Using direct access methods, malicious applications can obtain data from storage devices, modify or infect other executable software, record keystrokes and more. Comodo advises the average user to leave these settings enabled:
- Physical Memory: Monitors your computer's memory for direct access by applications and processes. Malicious programs attempt to access physical memory to run a wide range of exploits - the most famous being the 'Buffer Overflow' exploit. Buffer overruns occur when an interface designed to store a certain amount of data at a specific address in memory allows a malicious process to supply too much data to that address. This overwrites its internal structures and can be used by malware to force the system to execute its code. (Default = Enabled)
- Computer Monitor: Comodo Client Security raises an alert every time a process tries to directly access your computer monitor. Although legitimate applications sometimes require this access, spyware can also use such access to take screen shots of your current desktop, record your browsing activities and more (Default = Enabled).
- Disks: Monitors your local disk drives for direct access by running processes. This helps guard against malicious software that need this access to, for example, obtain data stored on the drives, destroy files on a hard disk, format the drive or corrupt the file system by writing junk data. (Default = Enabled)
- Keyboard: Monitors your keyboard for access attempts. Malicious software, known as 'key loggers', can record every stroke you make on your keyboard and can be used to steal your passwords, credit card numbers and other personal data. With this setting checked, Comodo Client Security alerts you every time an application attempts to establish direct access to your keyboard. (Default = Enabled)
Checkbox Options
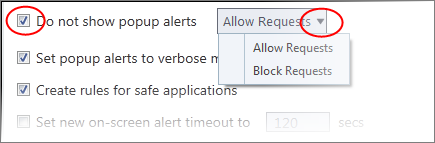
- Do not show popup alerts - Configure whether or not you want to be notified when the HIPS encounters malware. Choosing 'Do NOT show popup alerts' will minimize disturbances but at some loss of user awareness. (Default = Disabled)
If you choose not to show alerts then you have a choice of default responses that CCS should automatically take - either 'Block Requests' or 'Allow Requests'.
- Set popup alerts to verbose mode - HIPS alerts provide more information and options for the user to allow or block the requests. (Default = Disabled)
- The application is on the safe list, a global white-list of trusted software.
- The application has a 'Trusted' rating in the local file list. See File List if you need more details.
- The file is published and signed by a trusted vendor. The 'vendor' is the software company that created the file. See Vendor List if you need more details.
By default, CCS does not automatically create 'allow' rules for safe applications. This helps to reduce resource usage, to simplify the rules interface by reducing the number of 'Allow' rules, and can reduce the number of pop-up alerts. Enabling this option instructs CCS to begin learning the behavior of safe applications so that it can automatically generate 'Allow' rules. These rules are listed in the HIPS Rules interface. Advanced users can edit / modify the rules as they wish.
- Set new on-screen alert time out to: How long a HIPS alert remains on-screen if it is not answered. The default timeout is 120 seconds. You may adjust this setting to your own preference.
Advanced HIPS Settings
|
Note: These settings are recommended for advanced users only. |
- Enable adaptive mode under low system resources - Very rarely (and only in a heavily loaded system), low memory conditions might cause certain CCS functions to fail. With this option enabled, CCS will attempt to locate and utilize memory using adaptive techniques so that it can complete its pending tasks. However, enabling this option may reduce performance in even lightly loaded systems. (Default = Disabled)
- Block
all unknown requests if the application is running - Prohibits execution of unknown applications if CCS is not running/has been shut down. This is option is very
strict indeed and in most cases should only be enabled on seriously
infested or compromised machines while the user is working to
resolve these issues. If you know your machine is already 'clean'
and are looking just to enable the highest CCS security settings
then it is OK to leave this box unchecked. (Default
= Disabled)


