Protected Keys
- Click 'Settings' > 'Containment' > 'Protected Objects' > 'Protected Keys'.
- Registry items in 'Protected Keys' cannot be seen, accessed or modified by applications running in the container.
- Adding important registry keys to this area will protect them from unknown and potentially malicious programs.
Open the 'Protected Keys' section
- Click 'Settings' on the CCS home screen
- Click 'Containment' > 'Protected Objects'
- Select the 'Protected Keys' tab
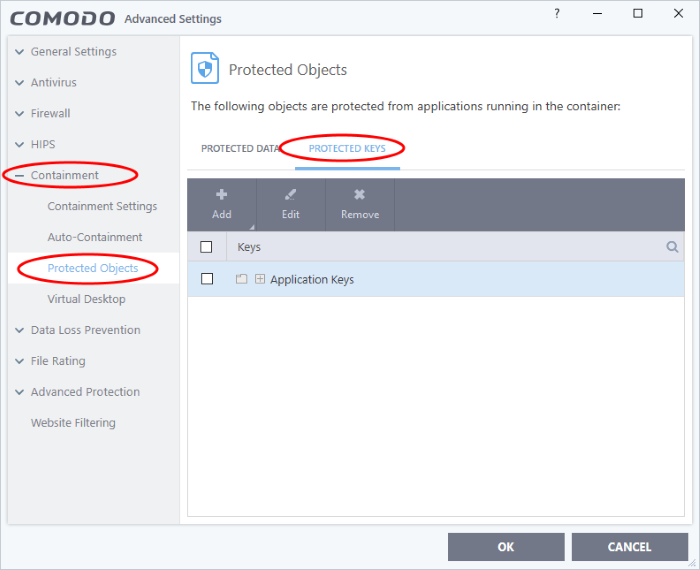
The buttons at the top provide the following options:
- Add - Select registry groups or individual keys that you want to protect
- Edit - Modify the path of the key or key group
- Remove - Delete the currently highlighted item
- Click the search icon at the far right to search for a specific item
Manually add individual keys or registry groups
-
Click the 'Add' button
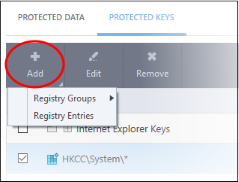
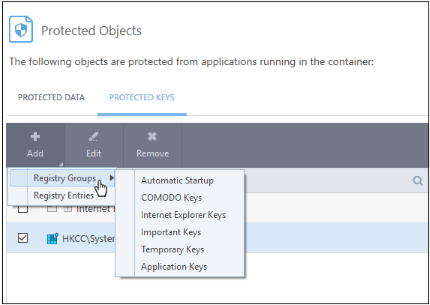
- Registry Groups – Select a pre-defined group of important registry keys. CCS ships with the following, pre-defined groups:
- Automatic Startup keys
- Comodo Keys
- Internet Explorer Keys
- Important Keys
- Temporary Keys
You can also create custom groups of the keys you want to protect. See Registry Groups in HIPS Groups if you want help on this.
- Click the 'Add' button > 'Registry Groups' > Select a key group from the list > Click 'OK'
- Registry Entries - Add individual keys to the protected list
- Click 'Add' > 'Registry Entries'
- Select the keys you want to protect in the left-pane
- Click the right-arrow to move them to the protected list:
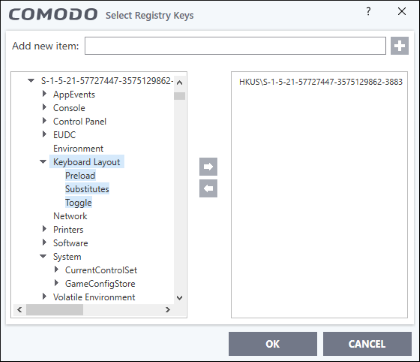
- Alternatively, you can type the key name in the field at the top then click the '+' button
- Click OK. All items in the right pane will be added to the protected keys list
Edit an item in the list
- Select the key from the list and click the 'Edit' button. The 'Edit Property' dialog will appear.
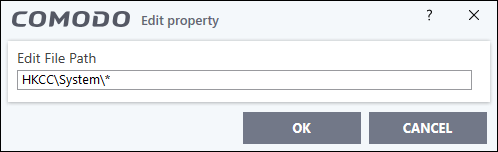
- Update
as required and click 'OK'.
|
Note: Click 'Settings' > 'HIPS' > 'HIPS groups' > 'Registry Groups' to edit registry groups. See Registry Groups if you need more help. |
Delete an item from Registry Protection list
-
Select the item from the list and click the 'Remove' button.
The
selected item will be deleted from the 'Registry Keys' protection
list.


