Protected Files and Folders
- Click 'Settings' > 'Containment' >'Protected Objects' > 'Protected Data'
- Items in 'Protected Data' cannot be seen, accessed or modified by applications running in the container.
- This fortifies files containing sensitive data from unrecognized and potentially malicious programs.
|
Protected Files and Protected Data
|
Add and manage protected data
- Click 'Settings' on the CCS home screen
- Click 'Containment' > 'Protected Objects'
- Select the 'Protected Data' tab
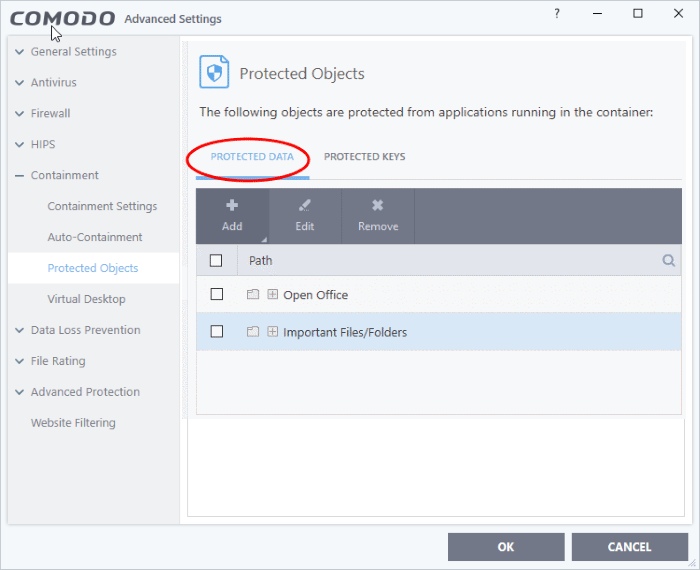
The buttons at the top provide the following options:
- Add - Select files/folders that you want to protect
-
Edit - Modify the path of the file or group
- Remove - Delete the currently highlighted item
- Click the search icon at the far right to search for a specific item
Manually add a file, folder or file group
- Click the 'Add' button
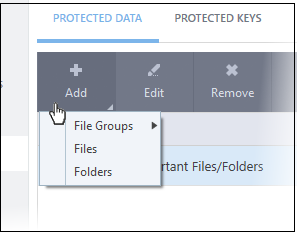
You can add items using any of the following methods:
Add a File Group
- Choose 'File Groups' from the 'Add' drop-down and select a file group.
- CCS ships with a set of predefined 'File Groups' which can be viewed in 'Settings' > 'File Rating' > 'File Groups'. You can also add your own file groups if required.
- For example, selecting 'Executables' allows you to exclude all files with the extensions .exe .dll .sys .ocx .bat .pif .scr .cpl, */cmd.exe, *.bat, *.cmd.
- Other categories include 'Windows System Applications', 'Windows Updater Applications', 'Start Up Folders' and so on. Each of these provide a fast and convenient way to apply a generic ruleset to important files and folders.
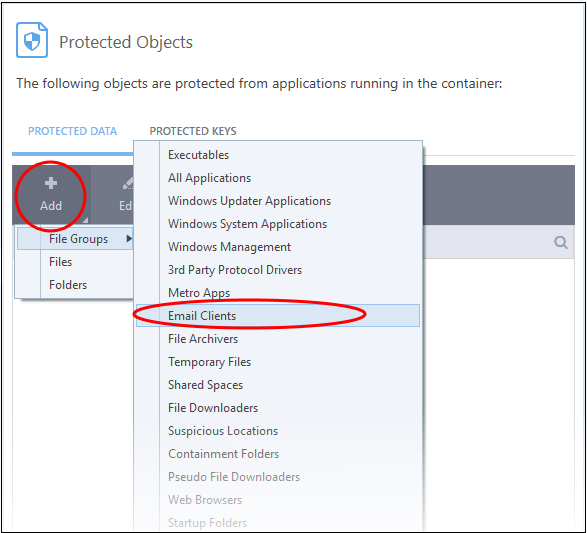
The selected group will be added to the 'Protected Files' list:
- Click 'Add' and choose 'Files' from the options:
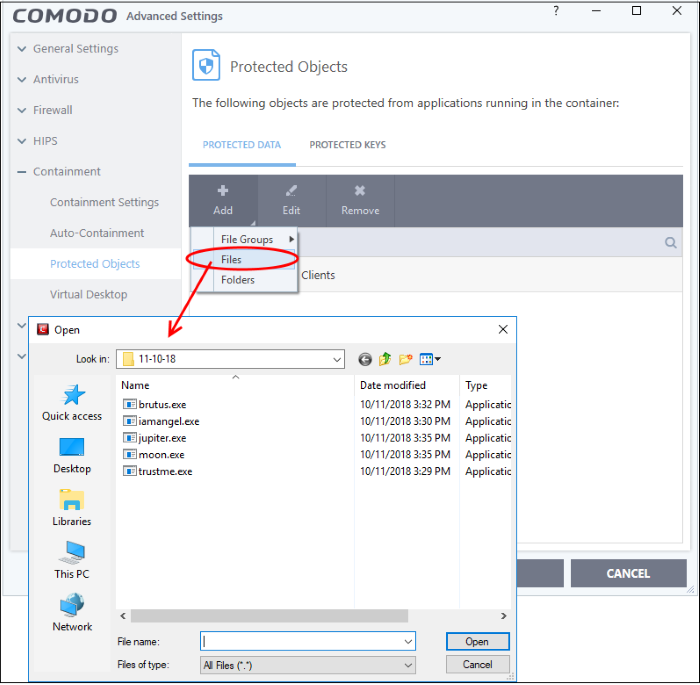
- Navigate to the file you want to add to 'Protected Files' in the 'Open' dialog and click 'Open'
The file will be added to 'Protected Files'.
Add a Drive Partition / Folder
- Click 'Folders' from the 'Add' drop-down.
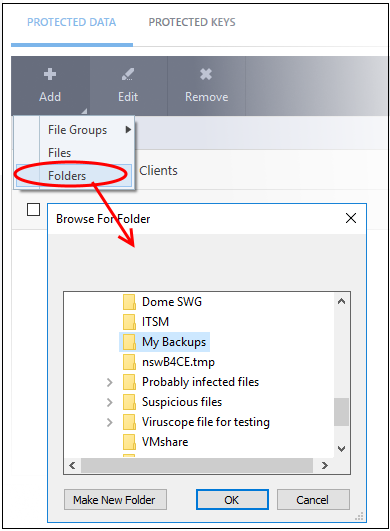
The 'Browse for Folder' dialog will appear.
- Select the folder/drive and click 'OK'. Repeat the process to add more items. The items added to the 'Protected Files' will be protected from programs that are contained.
Edit an item in the Protected Files list
- Select the item from the list and click the 'Edit' button. The 'Edit Property' dialog will appear.
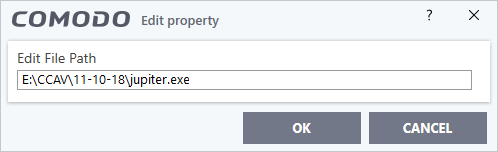
- Update as required and click 'OK'
Delete an item from Protected Files list
- Select the item from the list and click the 'Remove' button
The selected item will be deleted from the protected files list.


